The Top 10 Security Issues Facing The Cloud With Their Solutions
A large number of enterprises, as well as small businesses, are preferring cloud platform over on-premises software. However, the security of data in the cloud is a major concern, holding them back from cloud adoption.
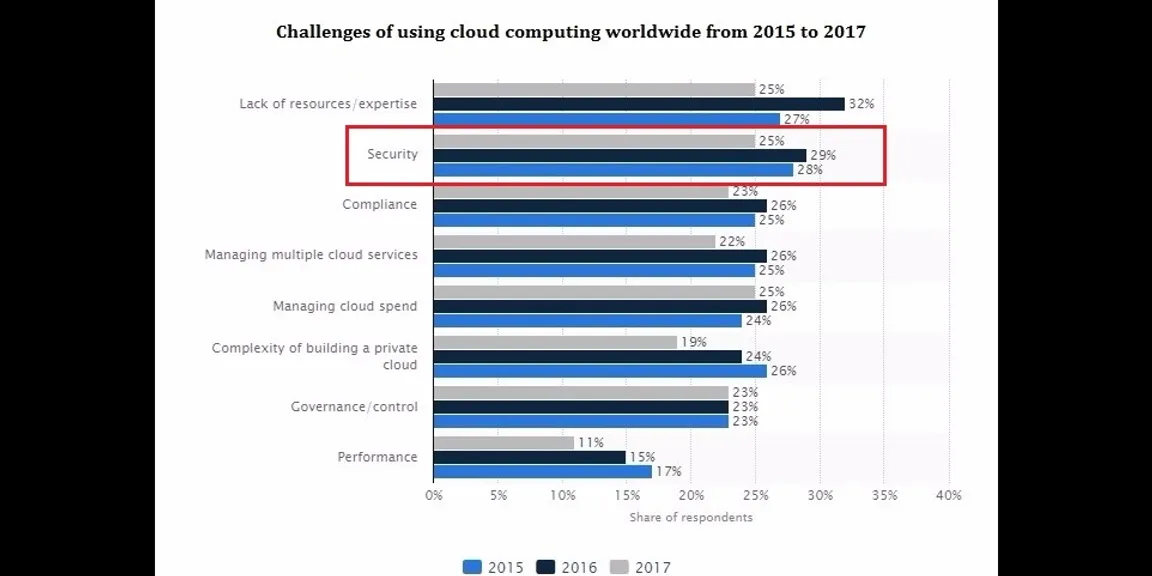
Both small businesses and large enterprises are reaping the benefits offered by cloud computing like cost-effectiveness, easy scalability, agility to make changes, etc., However, with the increased cloud adoption rates, the cloud computing security issues have enhanced in the existing computing platforms, networks, intranets, and internet in enterprises. Your data moves out of the well-built and carefully constructed security perimeter of your company, leading to security threats. The below graph shows the challenges of using cloud computing with security as one of the major challenges.

© Statista 2017
It is therefore important to use due diligence before selecting your cloud provider. You need to ensure that your provider has sufficient systems set up to overcome the security challenges facing the cloud. Even businesses are investing money in additional security features for Cloud computing.

Percent of total respondents, N=283 professionals IT at companies using cloud computing , Source: Clutch 2017 Annual Cloud Computing Survey
Here are the top ten cloud computing security risks.
1. Data Breaches
A data breach refers to a hacker stealing, using, or releasing sensitive information. It also occurs when someone by mistake exposes data to unauthorized users. As per a study conducted by Ponemon Institute, over 50 percent of the IT and security professionals who were surveyed, believed that their company’s security measures to protect data on cloud services were low. Nine scenarios were taken, after evaluation of which it was found that the chances of the overall data breaching were three times higher for businesses that utilized the Cloud than those that didn’t.
As per 2017 Thales Data Threat Report, which is based on a survey conducted by 451 Research, 68 percent of the respondents have faced a breach with 26 percent facing a breach in the last year; both the numbers rising from the last year.

To ensure security, data should be encrypted, with clearly defined roles for managing the encryption keys.
2. User Authentication
You should allow access to your data stored in the cloud to only authorized persons, making it crucial to restrict as well as monitor the one who accesses the company's data. For the purpose of user authentication, organizations should be able to see data access logs and audit trails to permit only authorized users to view the data. These access logs and audit trails also have to be protected against threats and managed till the company requires it.
3. Compliance
While cloud vendors continue to evolve, some haven't matured their security operations to a level that fit the requirements of all the organizations. The architecture of your cloud environment is crucial, and you have to consider the data storage regulations in the country you are in.
For example, a healthcare provider considering securing patient-related medical data on a public cloud has to verify whether the cloud solution is HIPAA compliant. A security infringement that results in noncompliance with an established law can lead to payment of fines, huge losses, legal action, and even punishments.
4. Negligence
Employee negligence and mistakes remain one of the biggest security challenges for the companies. Employees may log into the cloud solutions from their smartphones, home tablets, PCs, and laptops, leaving the system vulnerable to many outside threats.
Moreover, data breach and other attacks can happen due to poor user authentication and weak passwords.
It is crucial to use key management systems for enhanced security, and ensure that the encryption keys cannot easily be found online. Using strong passwords and multi-factor authentication can also help address the issue.
5. Malware
Malicious code can be injected into the cloud services, and attackers can eavesdrop, get your sensitive information, manipulate data and steal it.
As per the Security Threats On Cloud Computing Vulnerabilities report by the East Carolina University, malware injection attack has become a major security concern in cloud computing systems, which can be prevented by using File Allocation Table (FAT) system architecture.
6. APIs
Application Programming Interfaces (APIs) and interfaces are used to interact with cloud services, which can, however, pose a threat to the cloud security. APIs help to customize features of the cloud services to fit business needs, authenticate, give access and affect encryption, thus leading to enhanced risk. As a result, APIs expose companies to various security issues related to confidentiality, integrity, availability, and accountability.
Adequate controls, security-focused code reviews, and an effective penetration testing can keep a check on the threats imposed by APIs.
7. Data Loss
Data loss can lead to significant damage to the business. There are chances that users can delete the data by mistake, or data may be lost due to natural disasters or terrorist attack. Cloud providers have the responsibility to build powerful physical data centers to save companies from data loss. They can distribute data and applications across various zones for added protection. Daily data backup, off-site storage and adhering to best practices in disaster recovery is essential. The IT team of a company can also protect data by establishing SLA that includes regular backup and encrypting of files.
8. Due Diligence
Companies that choose this platform without fully understanding the cloud environment and its associated risks may encounter various challenges. Security risks can arise if a company’s development team isn’t aware of the cloud technologies. You need to use due diligence when you are trying to migrate to the cloud or merging with another company in the cloud. Proper training and management to prevent mistakes and errors become more critical in the cloud.
9. Employees’ Threat
Businesses using cloud services wouldn’t know about those employees who can cause harm to a company's data. For example, a salesperson being hired in a competitor’s company can download a report of all the customers’ contacts, upload the data to his own cloud storage and misuse it.
Even the current employees can take unauthorized access to a company’s cloud-based services to get information like customers’ accounts, financial forms, and other sensitive data. He can even manipulate the data or destroy the whole infrastructure.
Companies can control the encryption process and keys, assign duties to different people and minimize access given to users. Proper logging, monitoring, and auditing administrator’s activities are also important.
10. System Vulnerabilities
Cloud platform has system vulnerabilities, especially those networks that have complex infrastructures and various third-party platforms. Risks also arise in case of multitenancy in cloud computing, where hackers can identify vulnerabilities or bugs. Regular vulnerability scanning, timely security patches, upgrade protocols and networking monitoring solutions can keep system vulnerabilities under check.
Conclusion
The risks related to the cloud computing are less severe, but still damaging. Cloud presents a huge opportunity for enterprise IT, but only if the security design of the system in question addresses these threats. To take the benefit of cost savings, companies may rush into cloud computing without a serious consideration of the security challenges. Both the cloud service provider and the company have to take efforts in making the cloud is safe enough from all the internal as well as external threats to ensure a strong mutual understanding between them. To incorporate security, it is important to limit your vulnerabilities, not let anyone have access to your encryption keys and comply with all the required laws and regulations.