

Managed DDoS Mitigation – How They Can Detect and Prevent Losses for Your Business
D-DoS (Distributed Denial of Service) attacks are becoming more assailing with the attackers using powerful and sophisticated tools. To prevent and take precautions, it is important for an organization to look for managed D-DoS mitigation providers.
Solutions for businesses of all sizes:
It is a misconception that a small business is not a potential target for D-DoS attacks. The cyber-criminals, initially were targeting only successful and large traffic websites but now are more interested to create a disruption for whatever reason. It could be a blackmail, a disgruntled employee, competitor’s act or anything.
If your business goes offline, the losses can be drastic money-wise and reputation-wise. There will be a drop-in sale as consumers look for alternatives. They understand the technical aspects and, in their confusion, will hesitate to do business with you under the presumption, they too might get affected.
Your site can improve speed:
Managed D-DoS mitigation assures you superior protection by hiding the IP address of the hosting server. They make sure your site is not affected even if a neighbor website has been compromised. In addition to prevention of attacks, the experts can ensure your website performs faster. They cache your static content as well as the dynamic content to make sure it responds fast to a genuine request.
What exactly happens in D-DoS attack:
Multiple attackers from different regions target a website with the aim to deny access to the genuine traffic and disrupt sales and services. The victim site gets traffic beyond its bandwidth capacity i.e. the requests are much more than what the server can handle. The requests come from different quarters simultaneously. The D-DoS attacks are done in three ways:
- SMURF: This method has now lost its effectiveness. Managed D-DoS mitigation services have built many successful strategies. In this method, the attacker finds a broadcast address of network devices and sends echo requests with a fake source address. However, nowadays, it is no longer a threat since the routers do not send packets to requests received to the broadcast addresses.
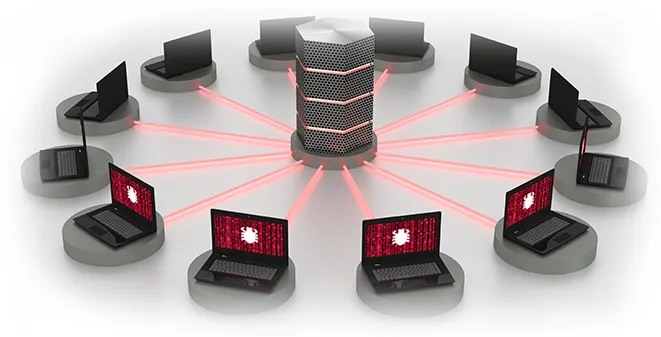
- Botnet: The most frequently adopted method of attack in the current times. Botnets can feign normal user access and makes it difficult to differentiate the genuine and fake customer. A botnet comprises of several computers that are infested with a virus or Trojan controlled by hackers.
- Amplification: In this type of attack, a request is sent to some random address with the IP address of the target website. This is done several times requesting for large content of data so that the victim’s bandwidth is unable to manage the incoming content. The response from the random sites causes the damage.
There are many more similar types of attacks that are targeted at businesses. the managed D-DoS mitigation providers are geared up to divert the malicious traffic requests. It may not be possible for your business to manage the attacks. The managed services utilize all the latest techniques like Content Delivery Networks to divert the healthy traffic.
However, it is also important to find out the right managed D-DoS mitigation provider to have effective solutions that your business may require. Some of the factors that you must consider include- which protection plan do you need? If your business has earlier been a target or attempts have been made by the cybercriminals, it is vital that you look for a comprehensive solution. The managed services come with proactive monitoring. They will curb any evolving threats at the root level before it transforms into any major issue. The providers use the newest tools to monitor the traffic, implement firewalls, automated detection, and alerts you any suspicious traffic movements.





