

More than 1 Billion Google users data is on risk
In October 2018, Google had announced that they are going to close its service Google Plus. Google had told that because of some bug, their 5 lakh(approx) user's data got leaked and they had fixed that error.
In October 2018, Google had announced that they are going to close its service Google Plus. Google had told that because of some bug, their 5 lakh(approx) user’s data got leaked and they had fixed that error.
My name is Rajshekhar Rajaharia and i am a individual security researcher and growth hacker. While working on few google products i found that using some very simple social engineering tricks anyone can access billions of google data and that is publicly available without any limit.
The real truth behind this is something else. In fact, Google is shutting down one more service besides Google plus, I will tell you name in the next Post. In fact, the reason behind shutting down these services, It’s almost 90% Individual Users and Business Users (Google Apps) data is at risk. I’m posting some Screenshots as a proof.
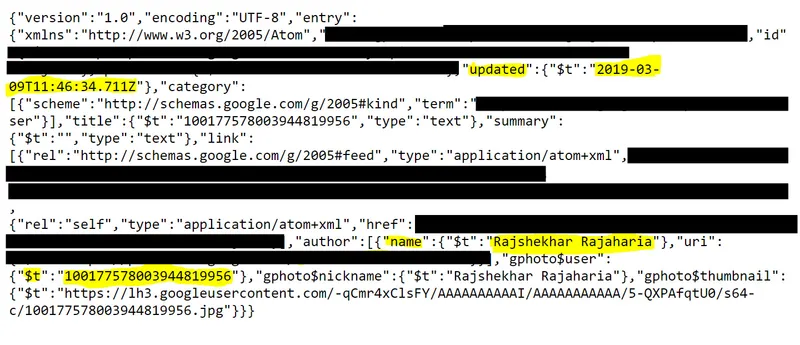
Google has more than 1 billion users. Because of these Google services, Information including any User’s Name, Photo, Google ID, Recent User Activity Date and Time (Very Sensitive Information), Gender, Skills, where the user is doing job or business, where the user is living and so on are publicly accessible without any limit. You can fetch any number of records without any limit or any credentials.
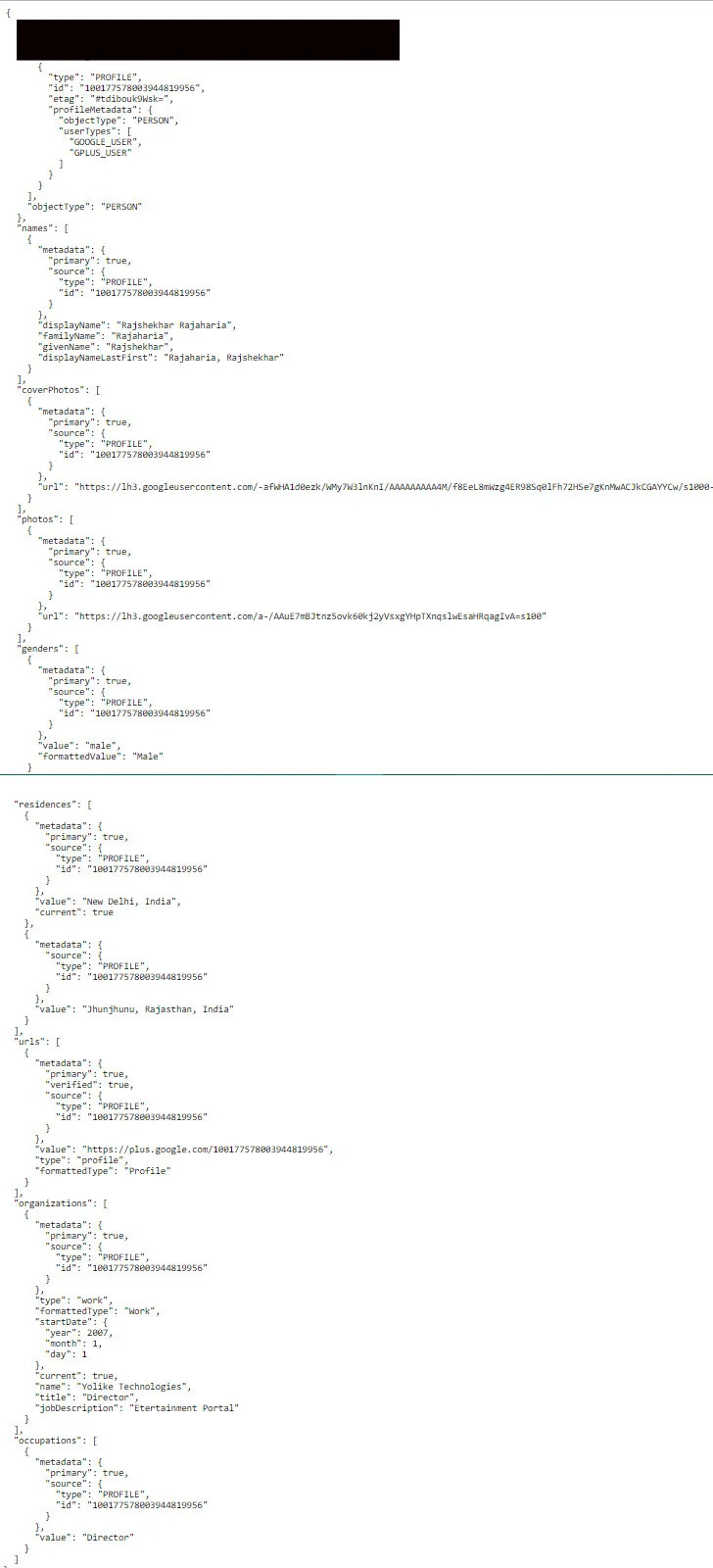
Although in today’s world data is most commonly used for Marketing and it is most dangerous for User’s data and privacy. Without user’s permission, one can reach to more and more people and it increases the risk of Fraud with the public.
The danger level increases when someone can access user’s data with date and time of recent activity including personal information
Using some Social Engineering Tricks Any Person can reach entire data easily because this data is publicly accessible without any limit or any credentials.
In the next post, I’ll share all the technical details.



![Top 10 Cheap Indian Press Release Distribution Services [Updated]](https://images.yourstory.com/cs/1/b3c72b9bab5e11e88691f70342131e20/LOGO-DESIGN-PR-INDIA-WIRE-03-1595693999405.png?mode=crop&crop=faces&ar=1%3A1&format=auto&w=1920&q=75)
