
This is a user generated content for MyStory, a YourStory initiative to enable its community to contribute and have their voices heard. The views and writings here reflect that of the author and not of YourStory.

Top 5 best strategies to optimize cloud security in 2020

This is a user generated content for MyStory, a YourStory initiative to enable its community to contribute and have their voices heard. The views and writings here reflect that of the author and not of YourStory.

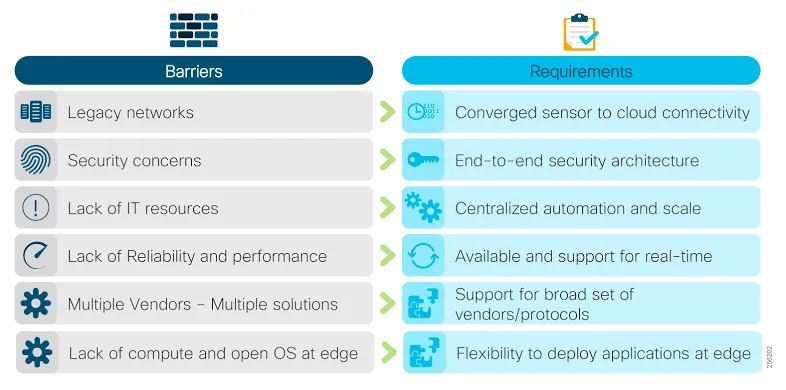
Cloud security takes a center stage in modern IT development to tighten the security for more sensitive information. The right tools can help keep information secure in the cloud. The appropriate integrations of cloud services manage security and privacy as a top priority. The risks associated with cloud computing such as loss of governance ownership, responsibility ambiguity, authentication and authorization, isolation failure, compliance and legal risks, security incidents, management interface vulnerability, application protection, data protection, personal data regulation, malicious behavior of insiders, business failure of the providers, service unavailability, vendors lock-in, incomplete data decision and many more can be minimized.
Expanding protective layers with user-level data security
A multilayered security approach helps protect your client's operations with different levels of security measures. The type of security layers that can be used in network defense includes web protection, patch management, email security and archiving, vulnerability assessment and analytics, antivirus software, data encryption, firewalls, digital certificates, anti-spam, and spam filters, privacy controls.
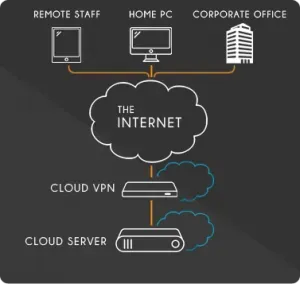
Use of virtual private cloud
As compared to the standard public cloud, the VPC tools help users get private with specially provisioned resources and maintain improved performance. The use of VPC, as we say, intranet service is completely isolated from others by means of virtualization. It offers very high data security with encryption chip security settings, tunneling, and private IP addressing. The user gets assigned cloud servers and virtual networks in VPC. With VPC it is not required to build your own infrastructure, it is fully managed by the cloud providers.
Implement cloud security policies
Implementing cloud security policies can make your business more productive and secure from the breach and other malware. Secure cloud account and creating secured groups, make free security updates available, restrict infrastructure access via firewalls, replace passwords with keys, tether the cloud, turn on auditing, and monitoring position.
Educate staff members
Conduct cloud security training to prepare your employees from risk from the cloud. Get staff cloud-ready.
Encrypt all kinds of data
The cloud service providers offer encryption services to less connected services, limited encryption of sensitive data, encryption services like these that can prevent unauthorized free access to your system, making it an effective data security method. Secure access by cloud cryptography to minimize network congestion can be the next option. Protecting data at rest and in access to the cloud security broker can also be counted.
Intrusion detection and prevention techniques
The probability of occurring intrusion increases with the enormous use of the cloud. It is a stronger strategy to provide security. The efficient, fast, and secure IDS collaboration is formed with the multi-layered network intrusion detection system and host intrusion detection system. In the intrusion detection system, cloud IDS captures packets from the network, analyzes them, and transmits reports to the cloud administrator on the basis of analysis.
Manage access to cloud applications
The proper management to access cloud applications give businesses flexibility, customizable cloud environments to support more efficient workflows, improve collaboration, and increase productivity.
If only Cloud computing offers many benefits to the organizations, but also, insufficient security and privacy protection yields in reputational harm, higher costs, and potential loss of business. Cloud Privacy is commanding much attention in recent years for every business.



